On September 27, 2024, the U.S. Department of Justice unsealed an indictment against three Iranian nationals described as IRGC employees, alleging a multi-year hacking campaign against U.S. officials, journalists, NGOs, and political campaign personnel. The operational pattern was familiar: spear-phishing, spoofed login pages, fraudulent mailboxes, VPNs, VPS infrastructure, and layers of hosting designed to obscure operator location.
What has been less visible is how that infrastructure was paid for.
Across BTC, ETH, BNB Smart Chain, LTC, and TRX, Caudena reconstructed roughly $184,000 in operational flows over four years, from October 2021 through October 2025. The amount is modest by cybercrime standards, which is exactly why the case is revealing. This does not look like ransomware revenue or an exchange-hack cash-out. It looks like a procurement budget: domains, VPS boxes, VPNs, ProtonMail accounts, disposable SMS verification, storage, hosting, payment processors, and swap routes.
The October 2025 OrangeMulator leak of internal IRGC documents appears to corroborate that interpretation. Department 40’s internal Excel sheet, 0-SERVICE-payment BTC.csv, reads like a procurement ledger: date, amount, service label, and destination wallet. The same categories that appear in the leaked records also surface on-chain. In this case, the blockchain did not merely show funds moving. It showed the financial operating system behind a cyber unit.
Threat-intelligence vendors track overlapping Iranian activity under several names — Charming Kitten, APT35, Phosphorus, Mint Sandstorm, TA453, and APT42 — and those labels do not always map neatly to internal Iranian structures. The OrangeMulator material makes the underlying picture clearer: “Charming Kitten,” as commonly used by the cyber community, appears here as a public umbrella for the IRGC-IO Counterintelligence Division, Unit 1500, Department 40, the unit associated with BellaCiao and CYCLOPS-family malware. The DOJ indictees do not appear in the leaked Department 40 personnel set and appear to represent a different IRGC-IO sub-cell. The on-chain footprint described below maps cleanly to Department 40.
The Operation Had a Finance Layer
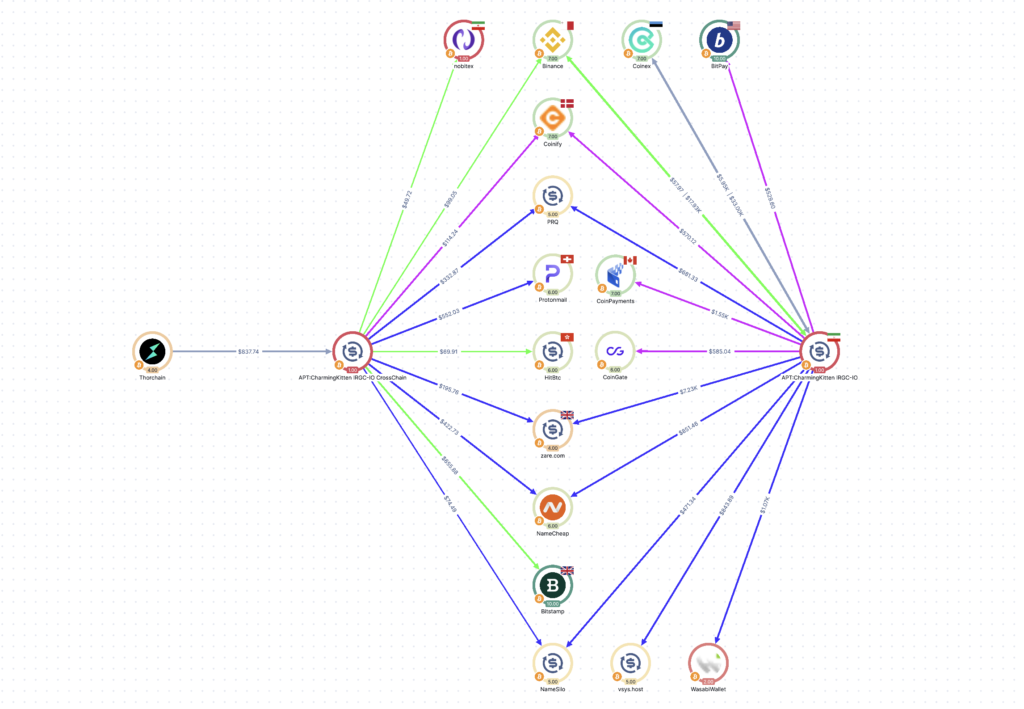
The footprint resolves into three layers: a core BTC procurement cluster, a BTC consolidation endpoint, and a multi-chain CrossChain cluster family. Operationally, the CrossChain family behaves as one system. Analytically, it appears as separate chain-specific surfaces.
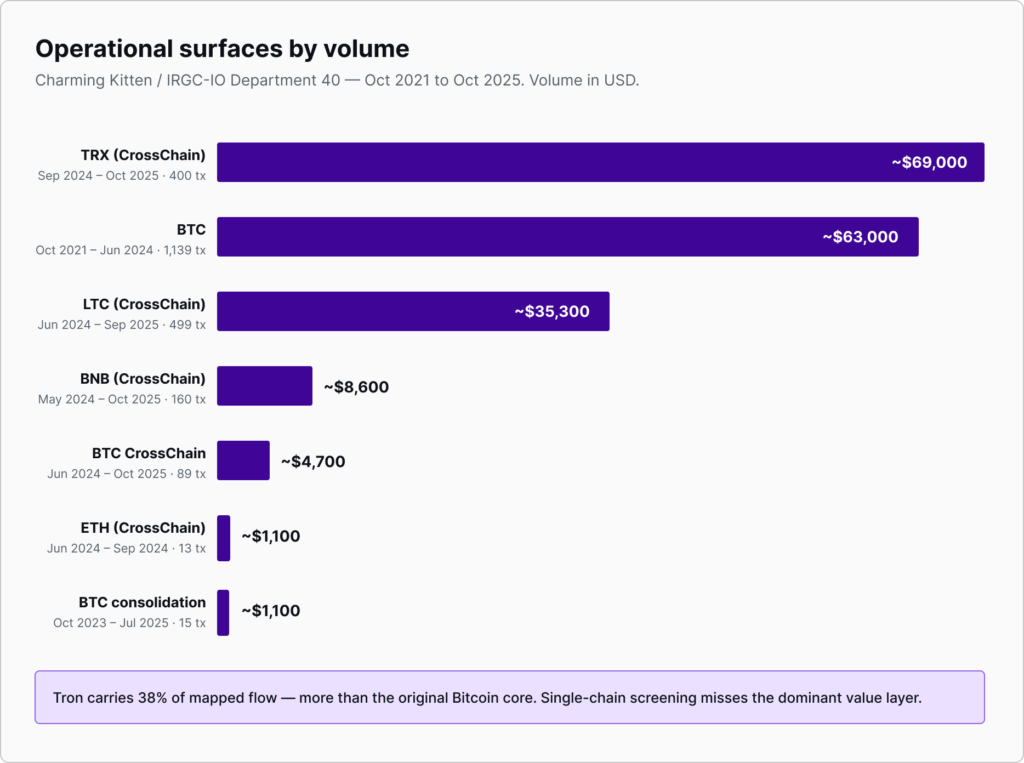
| Operational surface | Chain | Function | Volume | Transactions | Active period |
|---|---|---|---|---|---|
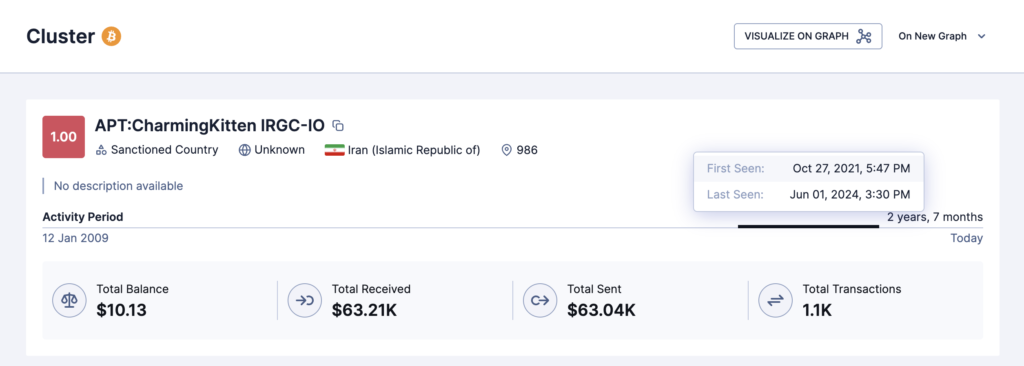
| APT:CharmingKitten IRGC-IO | BTC | Core receipt and operational vendor spending | ~$63k | 1,139 | Oct 2021 – Jun 2024 |
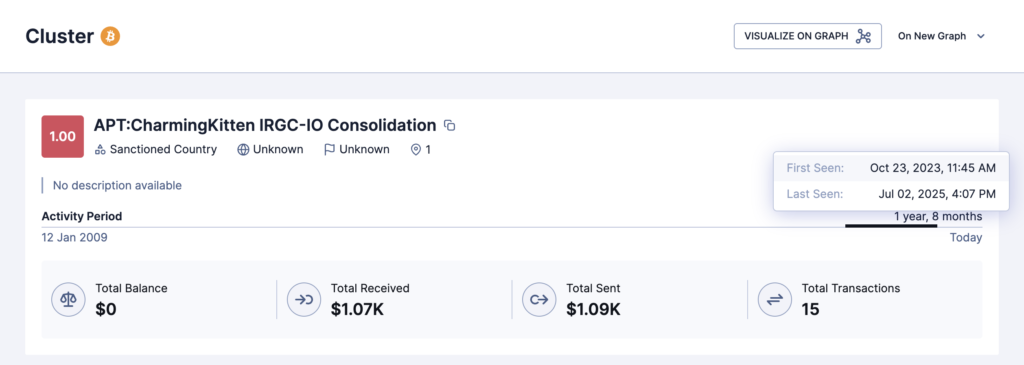
| APT:CharmingKitten IRGC-IO Consolidation | BTC | Aggregation endpoint | ~$1.1k | 15 | Oct 2023 – Jul 2025 |
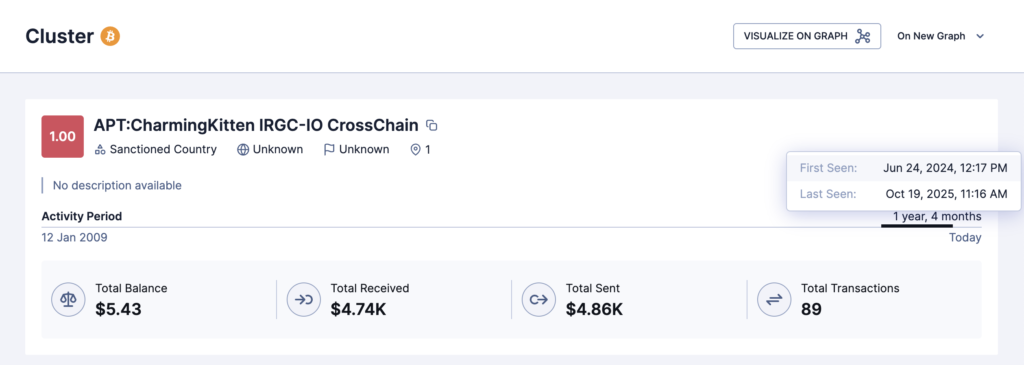
| APT:CharmingKitten IRGC-IO CrossChain | BTC | Cross-chain receipt and vendor continuity leg | ~$4.7k | 89 | Jun 2024 – Oct 2025 |
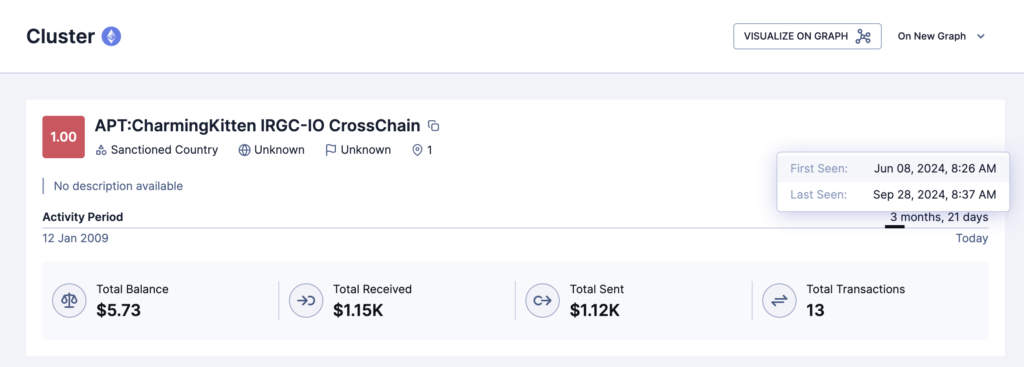
| APT:CharmingKitten IRGC-IO CrossChain | ETH | Bridge-aggregator entry point | ~$1.1k | 13 | Jun 2024 – Sep 2024 |
| APT:CharmingKitten IRGC-IO CrossChain | BNB | Fan-out operational leg | ~$8.6k | 160 | May 2024 – Oct 2025 |
| APT:CharmingKitten IRGC-IO CrossChain | LTC | BTC-alternative operational channel | ~$35.3k | 499 | Jun 2024 – Sep 2025 |
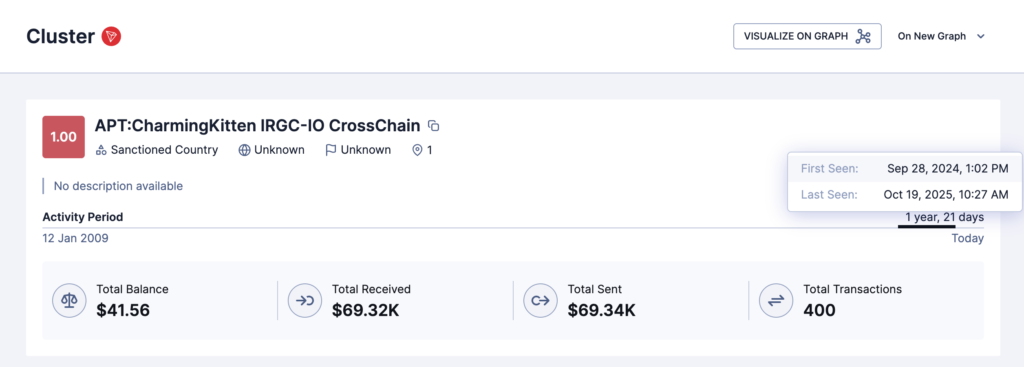
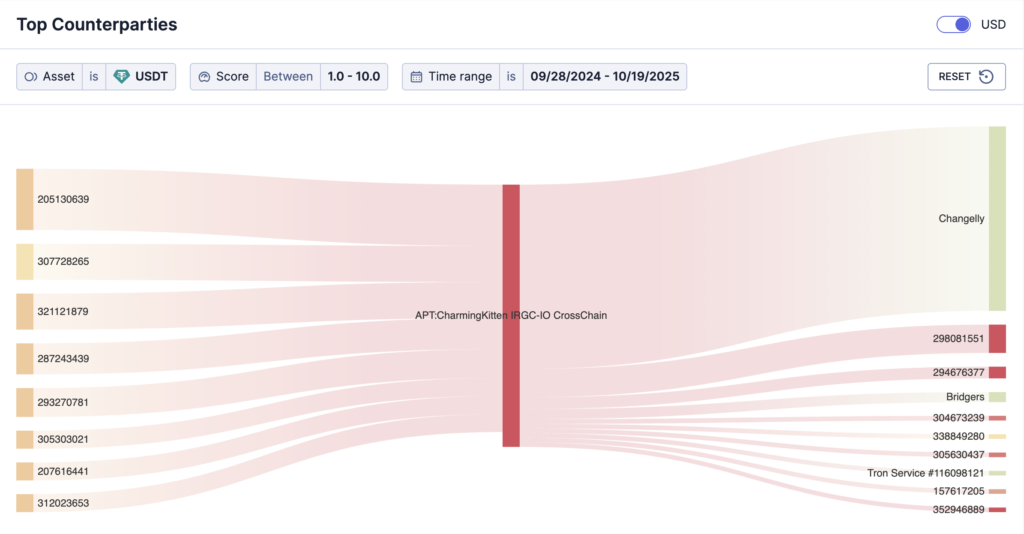
| APT:CharmingKitten IRGC-IO CrossChain | TRX | Dominant USDT cash-out and routing channel | ~$69k | 400 | Sep 2024 – Oct 2025 |
The structure is deliberately compartmentalized. The core BTC cluster handled the first era of procurement. The consolidation cluster gathered residual value. The CrossChain family took over in 2024, distributing activity across five chains and several swap services. The addresses changed, the chains changed, and the routing changed — but the procurement pattern remained consistent.
Bitcoin Was the First Checkbook
From October 2021 to June 2024, Charming Kitten’s procurement ran primarily through Bitcoin. Three exchanges dominated identified funding into the core BTC cluster: Coinex at approximately $34,247, Binance at approximately $22,201, and MEXC at approximately $2,040. Together, they represented 96.6% of identified inflow. A fourth source, Union Chain, contributes a smaller aggregate across the cluster set and is assessed as Changelly’s BTC-side settlement infrastructure rather than a separate operational counterparty.
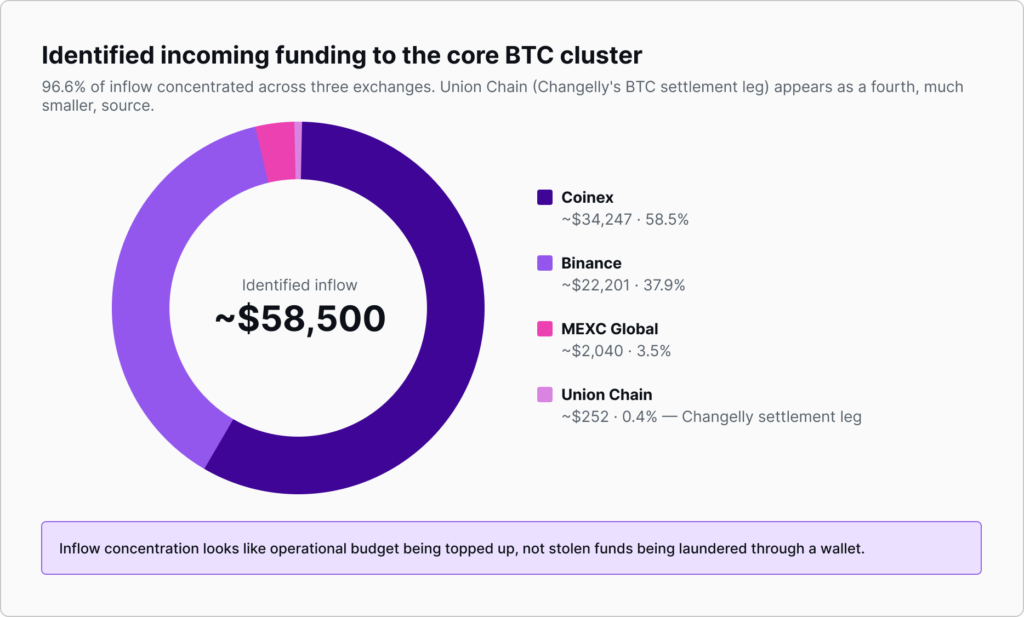
The funding pattern looks like an operational account being topped up and spent down. The leaked Department 40 ledger reads the same way, with concise internal labels such as “domain ecomonist,” “host wazayef,” “Domain #28,” “haji,” and “view for Idf(morteza).” These are not laundering notes. They are procurement notes.
The largest spending category was hosting and anonymity infrastructure. On-chain, Caudena identified payments to PRQ, vsys.host, TheOnionHost, NameSilo, CheapPrivacy, Doublehop, Colo House, Layer Servers, Xenspec, and Compevo. The leaked Service.csv expands the picture further, showing Department 40 procurement through dedistart.com, edis.at / edisglobal.com, imprezahost.com, my.nocix.net, pq.hosting / privatealps.net, redswitches.com, BlueVPS, ultahost, operavps, thcservers, zare.com, shinjiru, modernizmir, FlokiNET, and superbithost.
PRQ is especially notable. Across the core cluster and the CrossChain BTC leg, Caudena attributes roughly $1,014 in PRQ payments. The leaked sheet shows individually invoiced PRQ-related domain purchases for gassam.se, Termite.nu, “Jesus’s Cross,” moses-staff.se, “Abrahams Ax,” and musalas-alqassam.se. PRQ’s presence is consistent with an actor operating under takedown pressure and seeking resilient infrastructure.
Domain, communication, and storage procurement was similarly systematic. NameSilo dominates registrations on the operator side, with NameCheap and modernizmir.net as secondaries. ProtonMail and Mega received payments across both eras, showing continuity through the June 2024 rotation. The leaked sheet also shows Department 40 as a heavy consumer of disposable SMS verification through smspva.com, onlinesim.io, pvapins.com, 5sim.net, proovl.com, sms-man.com, and grizzlysms.com, often tied to throwaway ProtonMail, Skiff, or dnmx mailboxes.
Payment processors and obfuscation services also appear. CoinPayments, CoinGate, and BitPay likely represent merchants accepting crypto through standard processor integrations. WasabiWallet received approximately $1,067 from the core cluster, indicating a deliberate CoinJoin obfuscation step. The cluster also sent funds back to exchange-like venues, including Coinex, Paribu, ChangeNow, and AeroSwap. A later LTC payment surfaces a Coins.ph deposit address.
The significance is not that these services are illicit. Many are legitimate providers used by ordinary customers. The significance is that an IRGC-linked operational cluster used them as part of a broader procurement stack.
June 2024: the CrossChain Rotation
In June 2024, the architecture changed. The core BTC cluster wound down, and the CrossChain family activated across BTC, ETH, BNB, LTC, and TRX. The timing is too tight to look like organic drift. It is better understood as a deliberate operational rotation.
The most important shift was not simply from one wallet to another. It was from a primarily Bitcoin-based procurement system to a multi-chain, swap-enabled architecture in which each chain played a different role.
Tron became the dominant value channel. The TRX address is the largest CrossChain surface, and native TRX activity understates the real flow because the important movement occurred in USDT-on-Tron. Inflows arrived as just-under-round-number stablecoin transfers — approximately $17,000, $10,000, $10,000, $8,600, $8,000, $5,000, $5,000, and $5,000 — consistent with structured OTC-style funding. The largest recurring feeder sent roughly $17,000 USDT between January and July 2025; Caudena does not assess that address as Charming Kitten infrastructure itself, but as a shared settlement address. The largest exit was Changelly, which received more than $50,000 USDT across multiple deposit sessions. Bridgers and SwftSwap handled secondary exits, including a TON hop on November 4, 2024.
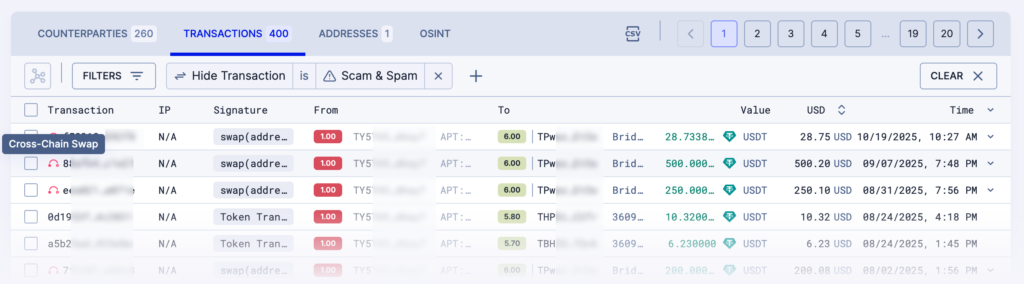
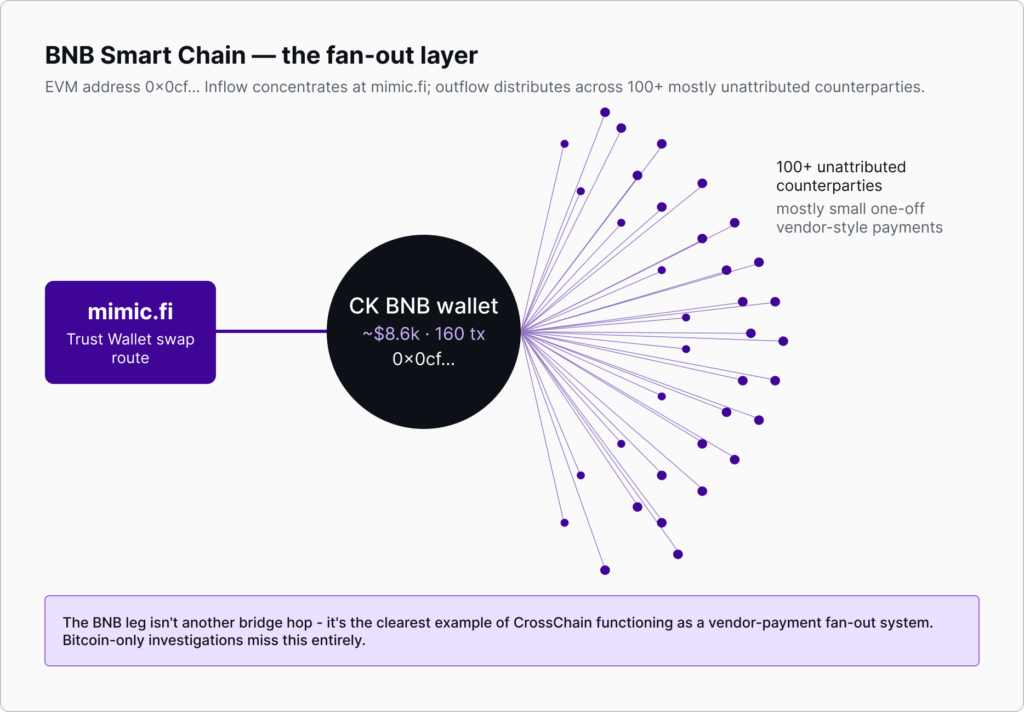
BNB Smart Chain exposed the vendor fan-out. The BNB leg uses the same EVM address as the Ethereum surface, handling approximately $8,600 across 160 transactions. The dominant inflow is from mimic.fi, a DEX route integrated into Trust Wallet swap flows. From there, the address fans out to dozens of mostly unattributed counterparties. This is the clearest example of CrossChain functioning as a vendor-payment distribution layer; a Bitcoin-only or Ethereum-only investigation would miss it entirely.
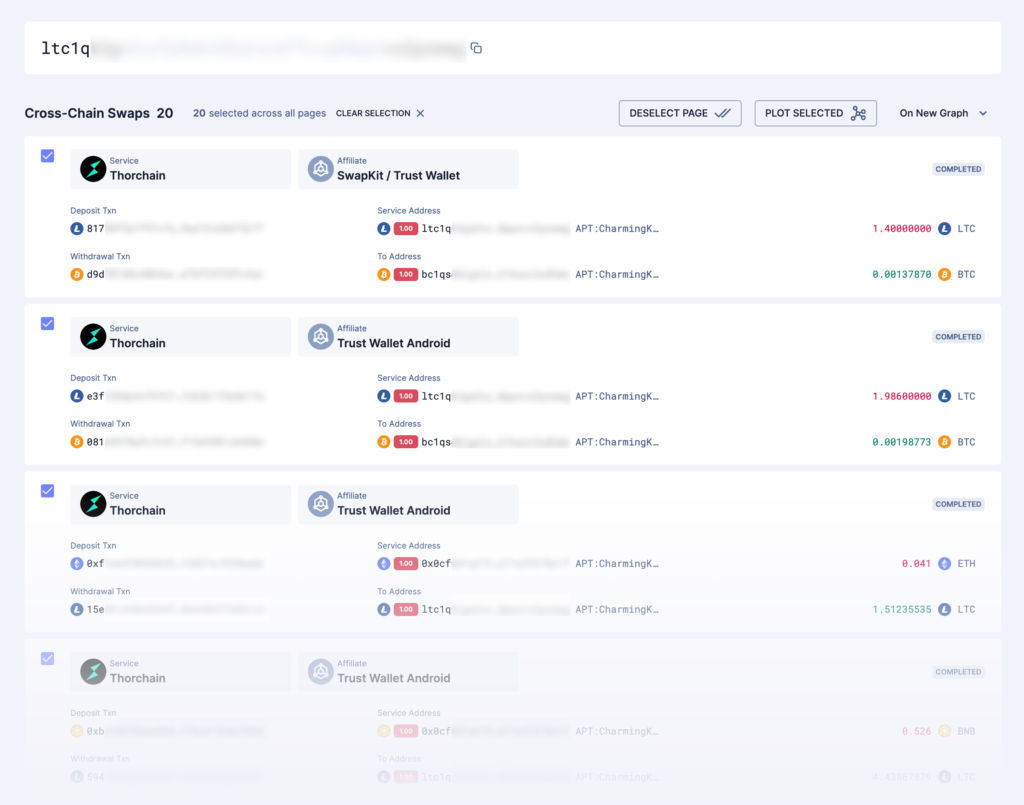
Litecoin became the BTC alternative. The LTC surface received approximately $35,326 across 499 transactions. HitBTC appears at first glance to be the dominant funder, but timing correlation against Changelly swap records shows that much of this is Changelly’s LTC-side settlement, not a direct HitBTC relationship. THORChain and Bridgers also appear in the LTC flow, and several THORChain inflows are not third-party funding at all but Charming Kitten’s own BNB-side activity routing into LTC through swap infrastructure.
Ethereum was small but analytically useful. The ETH surface handled only about $1,147 across 13 transactions, but its counterparties — Biconomy Hyphen, THORChain’s Ethereum router, and Rango/Stargate — reveal the bridge-aggregator entry layer.
Bitcoin CrossChain preserved vendor continuity. The BTC CrossChain address continued paying vendors visible in the core era, including ProtonMail, PRQ, and Mega. The addresses changed, but the procurement stack did not.
What the Procurement Bought
The on-chain ledger shows what was paid for in financial terms. The leaked Service.csv supplies the literal “for service” labels, mapping those payments to named operations and personas.
One of the clearest examples is Moses Staff, a persona presenting as a pro-Palestinian leak-and-shame group. Procurement records connect it to moses-staff.io, .to and .se plus TOR variants, NameCheap and PRQ domains, TheOnionHost TOR hosting, CloudNS DNS, ProtonMail, an ImprezaHost VPS at 95.183.51.49, and Comodo PositiveSSL via superbithost.
Abrahams Ax, an anti-Israel persona, appears in connection with PRQ and ImprezaHost infrastructure, including kundcenter.prq.se, an ImprezaHost VPS at 95.183.53.24, and the persona email [email protected].
The records also show Hamas / Al-Qassam-themed false flags, including gassam.su, gassam.se, host-qassam, cloudns-qassam, musalas-alqassam.se, and musalas.se, with payments through PRQ, xuid.ru, and privatealps.net. Israel Talent appears as a recruitment lure targeting Israelis, supported by TheOnionHost VPS infrastructure. AMEEN ALKHALIJ appears as a UAE security-personnel recruiting front whose live web log is present in the leaked material.
Additional procurement names include Termite, Jesus’s Cross, Wazayef-Halima, Dreamy Jobs, Cavinet, SecNetDC, Tecret, KanPlus, BBM, Kashef, Ofogh-SMS, and Blue-Payam.
Several BTC entries also tie payments to victim-side reconnaissance. The cleanest is the October 8, 2023 row labeled “view for Idf(morteza), $5” — a small payment that, in context, reads as a direct on-chain receipt for Israeli-defense reconnaissance.
Trust Wallet Android: the Behavioral Fingerprint
Every cross-chain swap in the mapped CrossChain family traces through Trust Wallet Android or a Trust Wallet-linked integration. THORChain records carry Trust Wallet Android / SwapKit affiliate tags. Bridgers records carry Trust-linked metadata. mimic.fi is the BNB-side route used by the same EVM address.
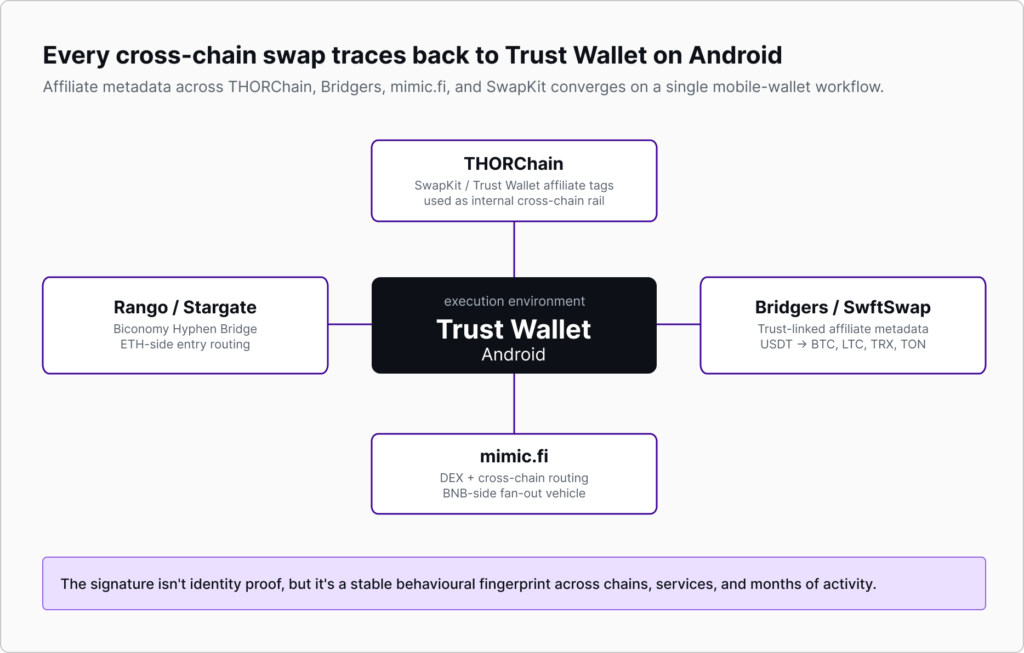
This is not identity proof, but it is a stable behavioral fingerprint across chains, services, and months of activity. Wallets can rotate, chains can change, and funding brokers can be replaced. Operational habits are harder to erase. The leaked operator-side ledger reinforces the workflow point: BTC payments are repeatedly tagged with internal codenames such as “haji,” while persona email accounts paying for hosting cluster around a small set of operator handles.
October 19, 2025: the Cutoff
On October 19, 2025, the CrossChain infrastructure went quiet in a compressed window. At 07:26 UTC, the BNB wallet made its final outbound transaction. At 07:27 UTC, the TRX wallet pushed residual value through Bridgers. At 08:16 UTC, the BTC CrossChain wallet consolidated UTXOs and sent remaining value to a vendor destination attributed to zare.com, confirmed in the leaked Service.csv as the host for “VDS – mmd hsn” at IP 5.226.137.136.
By the end of the hour, BTC, BNB, and TRX were silent; the LTC and ETH legs had already wound down. Three independent chains stopped within roughly fifty minutes. That is not market noise. It is a deliberate wallet-burn rotation, and it aligns with the OrangeMulator leak that publicly named Abbas Rahrovi, Mohammad Najafloo, and Mohammad-Erfan Hamidi-Aref as Department 40 leadership and infrastructure managers.
The cutoff does not produce a clean successor trail. The known Tron feeder had already stopped funding the wallet months earlier, and from mid-July onward the operators appear to have been spending down balances. Forward tracing after the cutoff reveals unrelated Tron-native customers, with no overlap in the Charming Kitten vendor set, swap-service pattern, or Trust Wallet Android signature. If Department 40 resumed operations, the successor was likely funded through a different broker and is not reachable from the mapped footprint.
Key Takeaways
USDT-on-Tron was the dominant value layer, not BTC or ETH. BTC/ETH-only screening would miss roughly 38% of the mapped flow.
BNB Smart Chain was the vendor fan-out layer. The BNB leg distributed payments to 100+ mostly unattributed counterparties via mimic.fi, making it invisible to single-chain investigations.
Apparent exchange relationships require settlement-layer analysis. HitBTC and Union Chain appear in the flow, but in key places they function as Changelly settlement legs rather than independent counterparties.
THORChain and Bridgers acted as internal routing rails. The same structural appeal that makes this architecture useful for large-scale laundering also makes it useful for small-scale procurement routing: chain agility, liquidity access, and fragmented visibility.
Compliance Implications
The mapped infrastructure carries sanctioned-country exposure tied to an IRGC-linked cyber-espionage operation. Three priorities stand out.
First, Changelly-side records are likely to be among the most important service-side artifacts. Caudena identified repeated USDT-TRC20 deposits from the mapped TRX wallet into Changelly addresses, with correlated LTC settlement via HitBTC and BTC settlement via Union Chain. Deposit records, account metadata, device data, IP logs, KYC artifacts, and order records may provide the most direct path toward identifying the operator or broker.
Second, the BNB fan-out should be treated as a target-development map. The BNB CrossChain surface sent funds to more than 100 mostly unattributed counterparties. Those counterparties should be screened for later exchange deposits, repeated vendor contact, and reuse in any post-October-2025 successor infrastructure.
Third, the vendor set should become a watchlist. Fresh high-risk or Iran-linked wallets paying the cross-corroborated vendor set — PRQ, NameSilo, NameCheap, ProtonMail, Mega, TheOnionHost, ImprezaHost, edisglobal.com, dedistart.com, my.nocix.net, smspva.com, zare.com, FlokiNET, and CloudNS — are strong leads for successor infrastructure.
Single-chain screening is insufficient. The Charming Kitten / Department 40 procurement stack moved through BTC, LTC, ETH, BNB, and TRX; used Trust Wallet Android swap integrations; converted USDT through Changelly; surfaced backend settlement through HitBTC and Union Chain; touched regional exchanges including Paribu, Coins.ph, and Nobitex; and burned the mapped wallets in a coordinated October 2025 cutoff aligned with public exposure of the unit’s leadership.
Caudena’s full cluster data — addresses, transaction-level evidence, swap-service records, Trust Wallet Android affiliate metadata, settlement-layer analysis, and the corroborating Department 40 procurement ledger — is available in Prism.
For compliance teams, law enforcement, regulators, and threat-intelligence analysts, contact Caudena to access the evidence pack.