In May 2019, Dutch and Luxembourg authorities seized the servers of BestMixer.io in what became the first large-scale law enforcement takedown of a cryptocurrency mixer. Over its single year of operation, BestMixer processed at least $200 million in Bitcoin, offering clients an explicit guarantee: full anonymity and the ability to bypass AML controls entirely.
Caudena has now fully reconstructed BestMixer’s address infrastructure — 146,520 addresses, a risk score of 2/10 on our scale, and $175.2M in confirmed BTC flows traced through Prism. We’ve mapped not just the service’s internal pool mechanics, but the post-mixing destinations that reveal who was actually using it.
The answer includes North Korean state-sponsored hackers, one of Japan’s largest exchange hacks, Russia’s largest darknet market, and a regulatory gap at Binance that turned it into BestMixer’s single largest exit point — responsible for $33.4M in net outflows alone.
How BestMixer Worked: A Three-Pool Architecture
BestMixer launched in May 2018 and quickly scaled to become one of the largest centralized mixers globally. Its core innovation, introduced in late 2018, was a three-pool architecture — Alpha, Beta, and Gamma — designed to give users tiered levels of obfuscation.
The Alpha pool was the baseline: a traditional “everyone-with-everyone” model where customer deposits were mixed with funds from previous sessions. The Beta pool added scale, combining customer funds with private reserves held by BestMixer’s operators and outside investors. The Gamma pool was marketed as the premium tier — an isolated reserve consisting solely of mixer-owned funds, including what BestMixer advertised as freshly mined bitcoins or coins previously cycled through third-party exchanges.
Each client was assigned a unique deposit address per mixing session. After depositing, funds were forwarded into the selected internal pool. For withdrawals, users could specify up to 10 destination addresses and — following a major update in early 2019 — configure individual parameters for each output, including the proportion of the total amount and a custom time delay. This feature significantly complicated naive transaction analysis, but as our Prism cluster reconstruction shows, it did not prevent full attribution of the underlying flows.
Crypto-Dusting: BestMixer’s Bold Marketing Gambit
One of the more unusual chapters in BestMixer’s history was its mass crypto-dusting campaign on October 23, 2018. The service distributed tiny transactions — carrying embedded advertising messages — to thousands of Bitcoin addresses. It was spam, broadcast directly on-chain, and it worked: BestMixer’s user base surged in the months that followed.
By spring 2019, with law enforcement scrutiny intensifying, the promotional campaigns ceased. Within weeks, the servers were seized.
Where the Money Went: Post-Mixing Flow Analysis
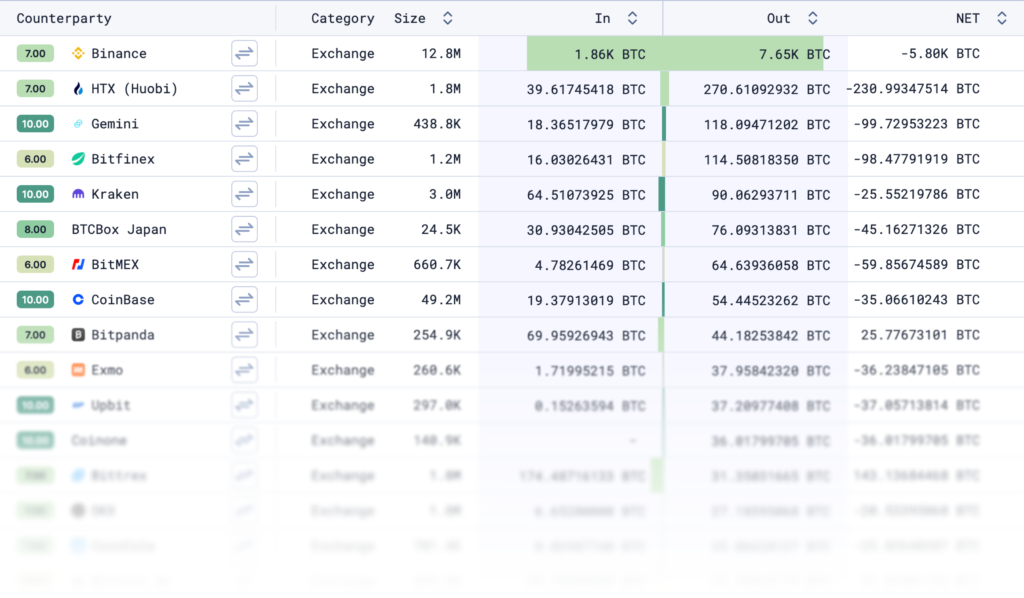
While the origins of funds entering BestMixer were often deliberately obscured, the destinations tell a much clearer story. Our Prism exposure analysis of BestMixer cluster shows that 66.2% of outgoing funds were directed to large centralized exchanges. A further 11.2% went directly to other mixing services — a chain-mixing pattern consistent with the most evasion-conscious users. An additional 8.4% exited through high-risk exchanges, and 1.1% was traced to sanctioned country exposure.
On the incoming side, the picture is equally revealing. 6.6% of all incoming exposure is directly attributable to Theft — funds arriving from known hack and theft clusters — with additional severe-risk inflows from OFAC-sanctioned entities (1.7%) and darknet markets (2.1%).
The most significant counterparty in our dataset is Binance — but not in the way you might expect. With a net outflow of 5,741 BTC ($33.4M) recorded in our cluster data, Binance wasn’t just a destination for BestMixer’s end users. Our analysis indicates that BestMixer’s operators were using Binance as a built-in laundering mechanism within the service itself.
The pattern works like this: BestMixer would aggregate customer funds across its internal mixing pools, then make structured deposits into Binance — always below the 2 BTC threshold that triggered identity verification during 2018–2019. Shortly after each deposit, the funds were withdrawn. The key effect: those coins now carried exchange provenance. Funds that entered Binance as post-mix Bitcoin exited as funds “from Binance” — a regulated, widely-trusted exchange — making downstream compliance screening significantly harder.
Caudena mapped hundreds of Binance deposit addresses that were reused multiple times across different mixing sessions, confirming this was systematic infrastructure built into BestMixer’s operation, not incidental user behavior. It was the service’s own operators running the legitimacy wash — on behalf of every customer whose funds passed through.
LocalBitcoins was another significant exit, with $1.85M in net outflows — reflecting the P2P platform’s popularity as an anonymity-preserving cash-out venue. CoinPayments, by contrast, appears in our data as a net sender into BestMixer, with 197 BTC in inflows versus only 8.6 BTC returned — suggesting it was being used as a payment intermediary feeding funds into the mixer.
Darknet Markets: Hydra
Two counterparty attributions stand out for their compliance significance. Hydra — Russia’s largest darknet marketplace and an OFAC-sanctioned entity — appears as a direct counterparty, sending 251.8 BTC ($1.13M) into BestMixer. Hydra’s funds largely flowed one way: only 9.6 BTC was ever returned, indicating BestMixer was used as a pure laundering step before funds moved elsewhere.
The presence of OFAC-sanctioned darknet market funds in BestMixer’s inflow set is a direct compliance flag: any institution that received post-mix BestMixer output had indirect exposure to sanctioned entities.
Mixer-to-Mixer Flows: Wasabi and Samourai
Beyond exchanges and darknet markets, 11.2% of BestMixer’s outgoing exposure went to other mixing services. Our counterparty analysis identifies WasabiWallet as the second-largest counterparty by cluster size, with a net outflow of 7.8 BTC from BestMixer into Wasabi. Samourai Wallet also appears as an outgoing counterparty.
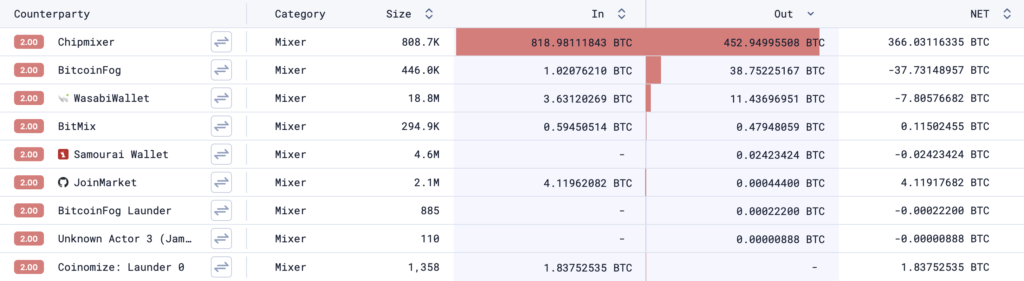
This mixer-to-mixer pattern — using BestMixer as a first-hop service before routing funds into CoinJoin-based wallets — is consistent with a layering strategy designed to break chain-analysis heuristics across multiple tools simultaneously. For investigators, it means that BestMixer attribution is often the starting point of a longer trace rather than the end of one. We’ve observed similar chain-mixing behaviour in our analysis of Coinomize, where multi-hop obfuscation across services was a defining operational pattern.
The Zaif Hack: Tracing $60 Million Through BestMixer to North Korea
The most consequential case linked to BestMixer is the 2018 Zaif exchange hack. On September 14, 2018, attackers compromised Zaif — a major Japanese exchange — and withdrew funds in BTC, BCH, and MONA. The primary Bitcoin address associated with the hack, 1FmwHh6pgkf4meCMoqo8fHH3GNRF571f9w, received 5,966 BTC — worth approximately $60 million at the time.
After a short obfuscation chain, the attacker began laundering proceeds through mixing services, routing roughly 1,500 BTC through BestMixer and additional volumes through ChipMixer. This co-appearance of BestMixer and ChipMixer in the same laundering chain is a recurring pattern — one we’ve also documented in our analysis of eXch and its role in the ByBit hack proceeds.
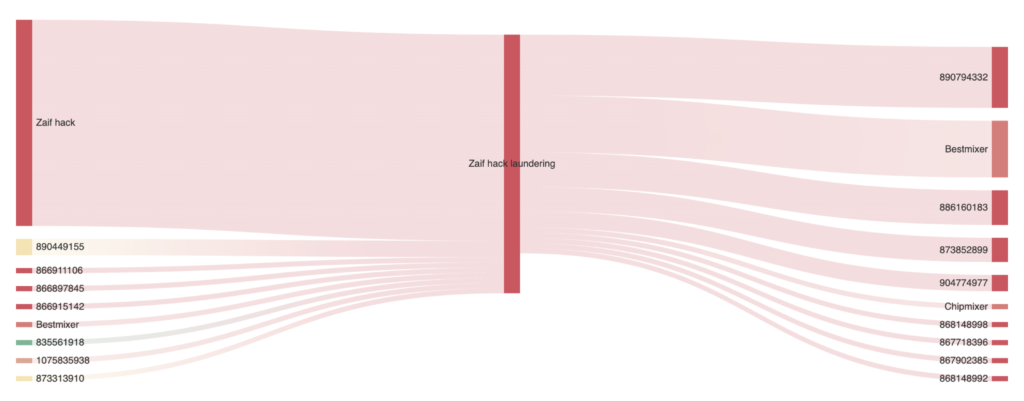
This is where Caudena’s demixing capabilities become critical. Our analysis of post-mix flows reveals that a portion of the funds withdrawn from BestMixer sessions were routed to clusters associated with North Korea–linked operators, specifically individuals tied to Sim Hyon Sop — a PRC-based representative of North Korea’s Korea Kwangson Banking Corp, designated by OFAC under Executive Order 13382 for orchestrating digital asset money laundering schemes to fund the DPRK’s weapons programs.
Another portion followed a different but equally revealing path: small increments were deposited into Binance addresses and subsequently re-aggregated into the same North Korea–linked cluster. Leveraging Binance’s minimal KYC requirements at the time, more than $4 million was transferred to attacker-controlled addresses via the exchange — consistent with the structured deposit patterns our Binance counterparty data shows at scale across the entire BestMixer cluster.
It is also highly probable that some funds underwent multiple mixing rounds — cycling through BestMixer and then ChipMixer — to add additional obfuscation layers. Despite this, the observable transaction chain linking the Zaif hack address through multiple dispersion phases to a single aggregating cluster associated with North Korean hackers remained intact. In total, this cluster accumulated approximately 6,000 BTC — corresponding closely to the full amount originally stolen from Zaif.
What BestMixer Teaches Us About Mixer Forensics
BestMixer represented a pivotal moment in the evolution of centralized mixing services. It combined large-scale liquidity — 146,520 clustered addresses, over 145,000 transactions processed — with sophisticated obfuscation features that were marketed explicitly at users who needed to evade compliance checks.
Its takedown demonstrated a fundamental limitation of centralized mixing: infrastructure-level anonymity does not protect services once operational control points — servers, logs, liquidity pools — are exposed to law enforcement.
But the deeper lesson is forensic. The post-mixing flow patterns, the consolidation behavior after the mixing procedure, and the reuse of exit infrastructure all create exploitable fingerprints. Caudena’s full reconstruction of BestMixer’s cluster — including its OFAC exposure, darknet market counterparties, and the Zaif-to-DPRK attribution chain — confirms that even sophisticated mixers leave behind enough signal for complete attribution. For context on coverage depth: independent academic research published at USENIX Security 2025 found that leading blockchain analytics platforms identify as few as 24.54% of BestMixer addresses. Caudena’s Prism cluster for BestMixer contains 146,520 addresses — a meaningfully different level of coverage.
Our BestMixer demixing capability is live in Prism and has been validated across multiple investigations. For compliance teams receiving funds with BestMixer exposure, for law enforcement tracing 2018–2019 theft proceeds, and for investigators following North Korea’s laundering infrastructure, historical BestMixer transactions are no longer a black box.
For more information on our demixing capabilities or to explore BestMixer cluster intelligence, book a demo with us.